Byos Secure Endpoint Edge™
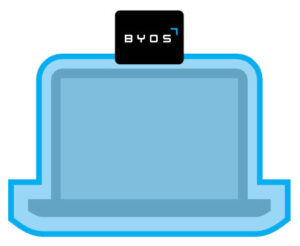
A small plug-and-play External Retransmission device providing “first hop” protection on untrusted Wi-Fi networks.
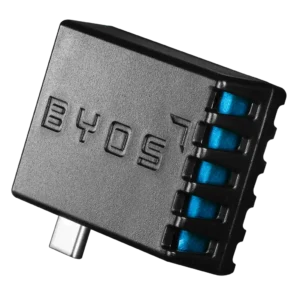
BYOS Secure Endpoint Edge 200

Byos Secure Endpoint Edge™ protects your laptop by isolating it from the network, making you invisible at a coffee shop, airport, or conference. It eliminates the attack surface and minimizes the blast radius of any attack trying to leverage lateral movement.
Attackers can’t bypass it because it’s independent from the OS, making it compliant with NSA’s CSfC requirements.
BYOS Secure Endpoint Edge 200 Device
Price range: $695.00 through $2,694.00
* License is required per device.
BENEFITS AND ROI
Microsegmentation at the Edge
Each device is isolated in a microsegment, blocking lateral movement and protecting against ransomware and unauthorized access.
Asset Isolation
With Byos assets are completely invisible on local networks, preventing discovery, fingerprinting, and unauthorized access attempts.

Plug-and-Play Deployment
Byos is agentless, connecting via USB-C, requiring no software or network changes, ensuring fast, non-intrusive deployment.
Core Capabilities
From a Security Perspective, Byos has three unique differentiators:
Inbound Network Attack Protection:
- “First-hop” protection across OSI Layers 1-5 through Hardware-enforced Isolation
- Obfuscating the protected device to be effectively invisible on the network

Outbound Traffic Protection and Control:
- Network Access Control (NAC)
- Route enforcement
- Traffic anonymization through layer 4+ data encapsulation and exit node enforcement

Centralized Management:
- Policy-driven access control per microsegment
- Byos-enforced IAM Conditional Authorization
- Secure remote access without endpoint exposure