Byos Secure Cluster Edge™
Byos Secure Cluster Edge brings powerful, hardware-enforced microsegmentation to the datacenter
The Secure Cluster Edge

Internet Isolated Access
Access resources on the server without having to expose the server to the internet.

Plug and Play
No network redesign or complex configuration required. Deploy in minutes and secure your assets instantly.

Server Rack Mountable
Deploy directly in existing datacenter infrastructure.

How the Cluster Edge works
Byos Secure Cluster Edge™ slots directly into your server rack, acting as a secure gateway between your workloads and the rest of the network. Each of its 10 downlink ports forms an isolated microsegment, with dedicated access controls, ensuring that traffic between segments is tightly controlled and monitored.
No reconfigurations. No software agents. No exposure.
Once installed, it creates a Zero Trust perimeter around each device or VM connected to it, effectively preventing lateral movement, reducing blast radius, and enabling dynamic policy enforcement – all without disrupting your existing setup
CORE CAPABILITIES
Secure Connectivity and Remote Access
Easier and faster updates or changes to the network without wiring changes, leading to reduced downtime

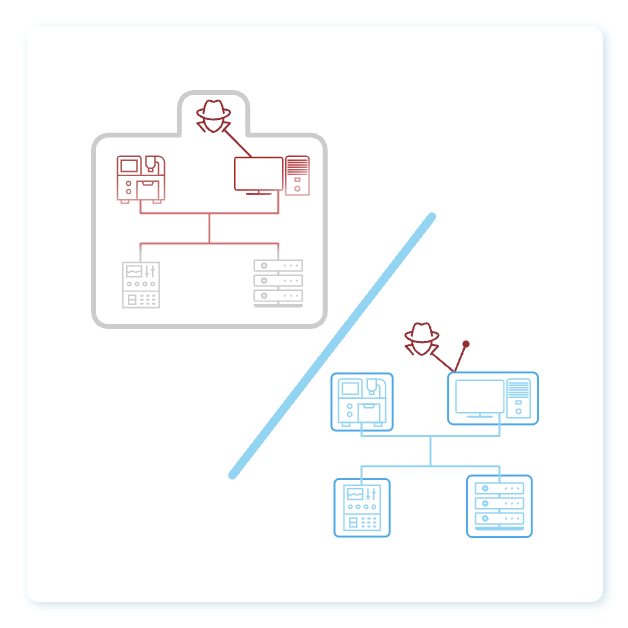
Eliminating Lateral Movement Exposure
Even if an intrusion occurs, the ability to limit lateral movement minimizes the potential impact and spread of a breach
Simplified Granular Third Party Access Control
Easily manage complex networks and safely enable granular access without compromising overall OT network security.

Benefits and ROI
Prolong Legacy System Life
Securely extend OT infrastructure lifespan by protecting legacy systems from ransomware and lateral movement.
Centralized Management & Control
Enable secure, policy-driven access to remote devices, including air-gapped systems, reducing operational costs.
Enhanced Data Collection
Get secure, flexible data access across your OT environment, including IoT, legacy, and OT devices.
FIPS Validated
Byos Cryptographic Module is FIPS 140-2 Validated. Visit the NIST CMVP website for more details – Certificate #4964

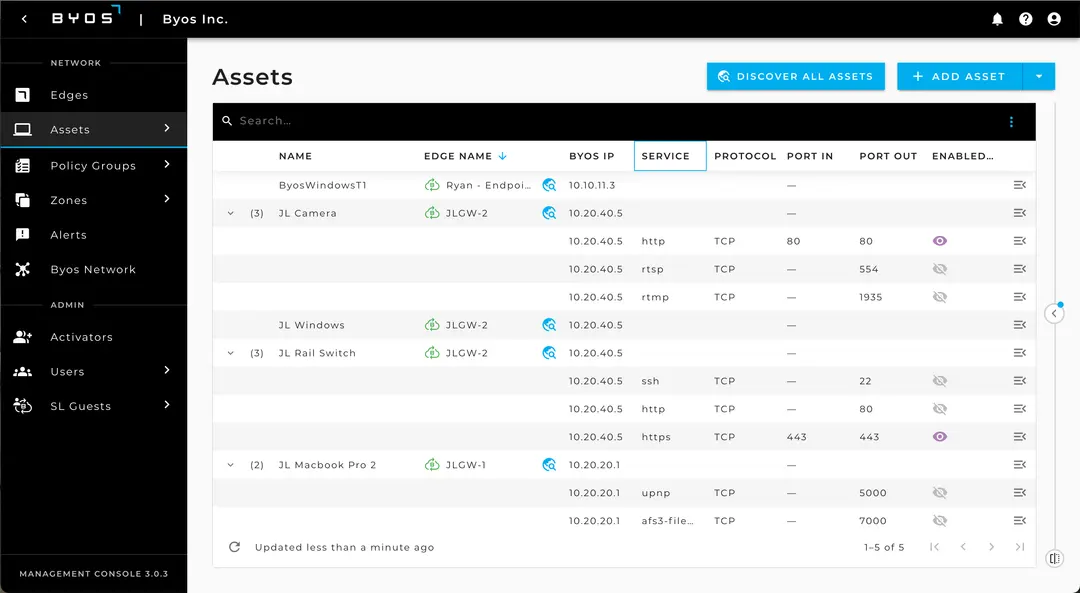
Byos Secure Networking Platform – How It Works
Byos Secure Lobby™ – the Data Plane
Secure Lobby™ is a Software-Defined Network (SDN) Overlay that allow Assets connected to Secure Edge™ devices to communicate between each other. It enables operators more efficient monitoring, troubleshooting, updating, and patching remotely, without exposing internal assets to the internet.
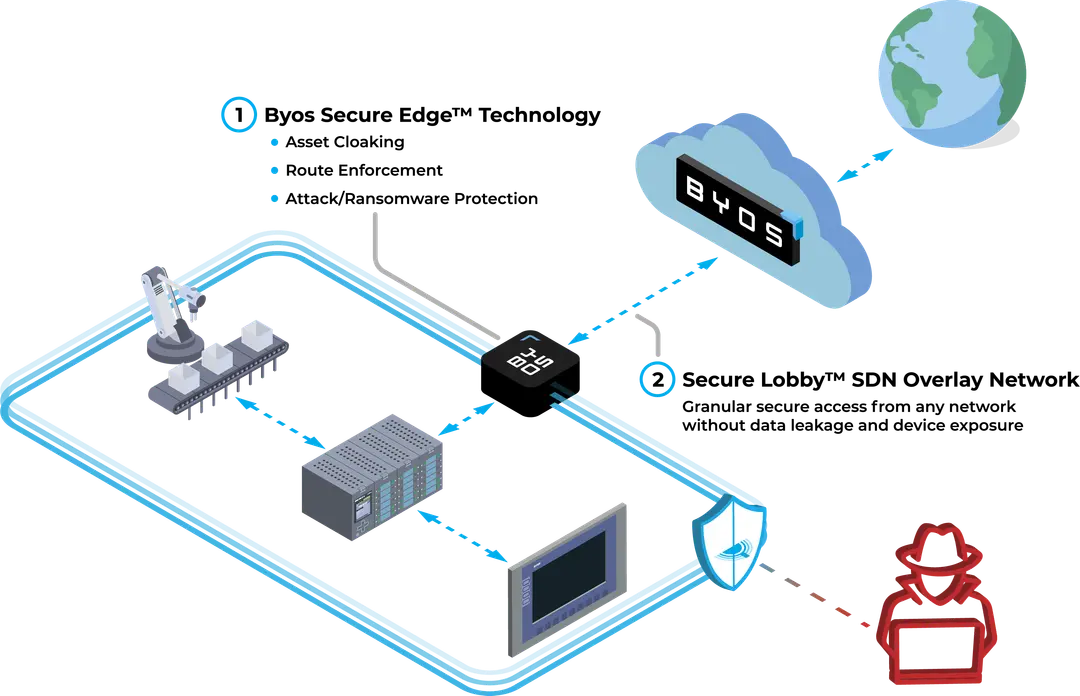
Byos Management Console – the Control Plane
The administration interface used for centrally managing all deployed Byos Secure Edge devices, with real-time policy pushing for instant control.