
Network Security Made Simple: Cloak assets with the Byos Secure Edge™, and easily manage your network using Byos Secure Lobby™
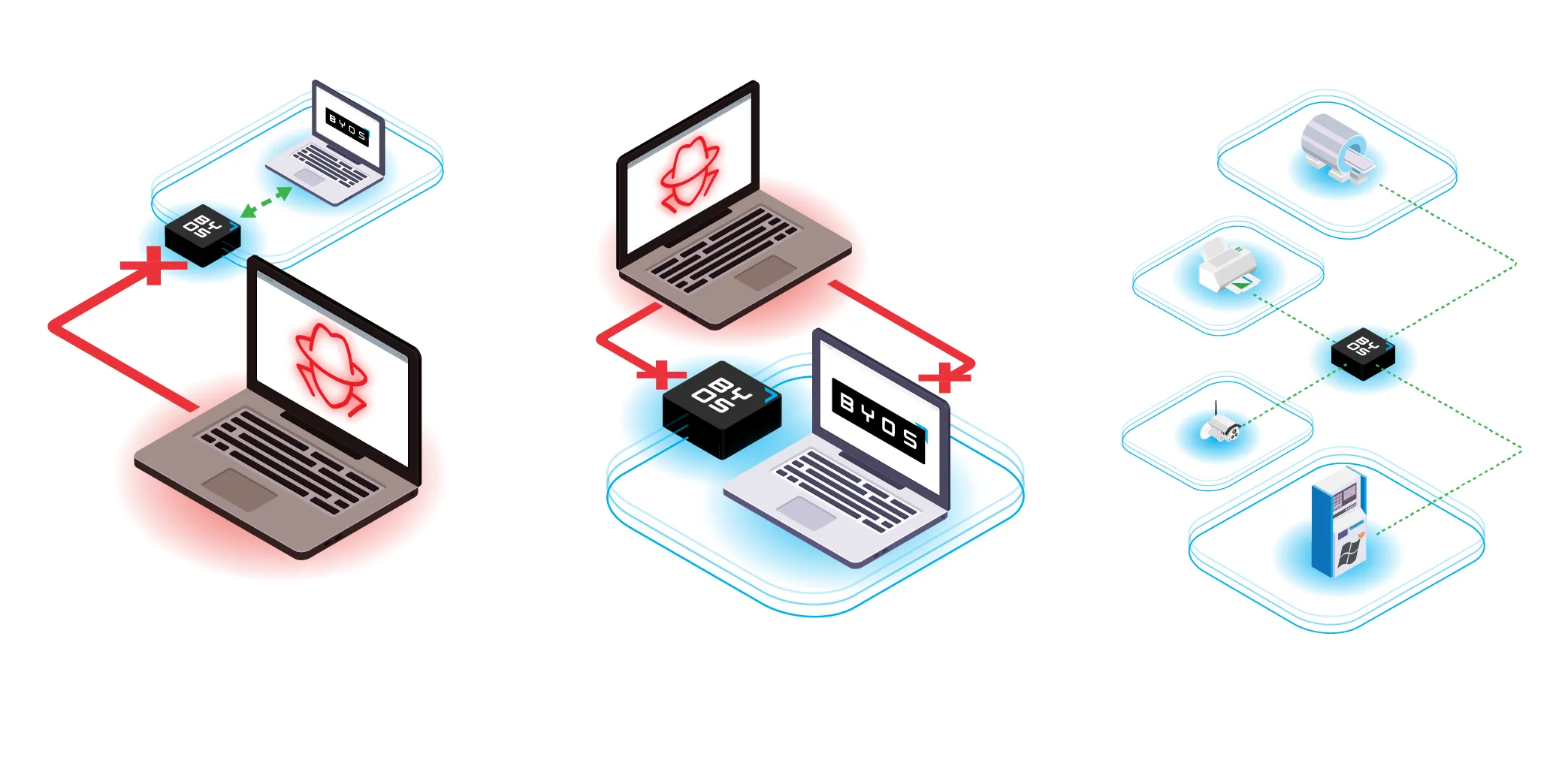

The most effective way to secure your network is to make every device undiscoverable and inaccessible – that’s entirely new!
BYOS lets you monitor and control the traffic at the outer edge, physically stopping attacks before they reach the asset.
BYOS runs independently from the asset and OS, providing a stronger containment strategy against attacks.
BYOS delivers device and OS-agnostic protection, minimizing the attack surface and broadening the coverage area.

No Compromises
Access everything without allowing access to anything!
BYOSwerx allows you to access any asset remotely, from and to uncontrolled networks. Simultaneously, those assets don’t have access to anything, are protected, and are invisible to the local network.
The BYOS Difference
DO YOU RELY ON VPN's TO PROTECT REMOTE WORKERS?
Access Purpose
BYOS
VPN's
Endpoint Protection
✔️ Protection, control and access
❌ Just about access
Traffic Direction
✔️ Secure Edge protects the endpoint and the traffic
❌ Protects the traffic, not the endpoint
Edge Filtering
✔️ Inbound and outbound traffic protected
❌ Only projects outbound traffic
Network Visibility
✔️ Drops unsolicited requests at the edge
❌ Vulnerable to network attacks despite encryption
OS Dependency
✔️ Endpoint invisible to the network
❌ Exposed to fingerprinting, enumeration, DDoS, etc.
Route Enforcement
✔️ Doesn’t depend on the OS
❌ Controlled by and dependent on the OS
Traffic Leakage
✔️ Enforces that all traffic passes through BYOS
❌ OS can communicate outside the VPN
Access Control
✔️ Prevents traffic leakage until Secure Lobby is established
❌ Leaks until VPN is connected
Key Mgt
✔️ Layer 2 granular control (Lobby On/Off, port/service)
❌ Layer 7, too broad (on/off only)
Architecture
✔️ Automated key management
❌ Requires manual key/config exchange
Micro segmentation
✔️ Decentralized protection at each Secure Edge
❌ Heavily dependent on remote VPN Terminator
